Tandem / Monero
Applying the privacy-preserving algorithms of Tandem to the usage of the Monero blockchain.
One challenge when using private keys is that if they get stolen the damage can be very big, especially when used in blockchains to protect funds. Sharing the private key between multiple entities can secure the usage a bit, but most algorithms don't give privacy. In the context of a privacy-preserving service like Monero, where the source and destination of a transaction are hidden, these algorithms would leak information about the user. Applying Tandem to transactions on the Monero blockchain allows to protect the private key in case of loss, while keeping the owner of the transaction private.
- Presentation
- Research papers
Introduction
With the upcoming Web 3.0 more and more services rely on private keys. This includes, but is not limited to, blockchains and identity management systems that allow a user to selectively disclose one or more attributes. Another element of Web 3.0 is decentralization, which makes it harder to revoke a stolen or lost private key.
The most common protections for these private keys include Wallets as a service like hardware wallets and hardware security modules. But these solutions all contain a single point of failure that can leak the private key or lead to abuse. To avoid a single point of failure, one can use threshold cryptographic solutions like Calypso or Sepior. However, for a service that is privacy preserving, these solutions leak the identity of the key user.
For this reason Tandem has been developed. It is a threshold-cryptographic solution like the ones cited above. But it does not leak the identity of the client, which is important when it is used for a service that is privacy preserving. The Tandem paper shows how to use this solution for Attribute-based credentials. In this setting a simple threshold-cryptographic solution can protect the key, but it will deanonymize the user.
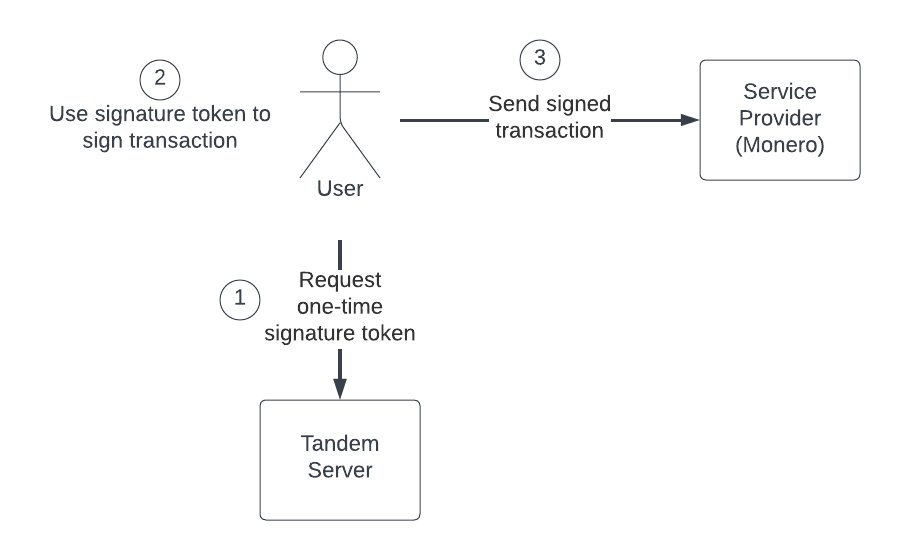
We looked at the Monero blockchain, which provides anonymous token transfers. These transfers are initiated with transactions that are signed by a private key. We show how to convert a Monero transaction into a Tandem-compatible protocol without the need to modify Monero. C4DT contributed to the elaboration of the protocols to be used between the client and the Tandem server. Pending to find partner support, we would like to test it on the Monero test network, and write a reference library in Rust.
Security and Privacy Engineering Laboratory
Security and Privacy Engineering Laboratory- Machine Learning impact on society
- Evaluating privacy in complex systems
- Engineering privacy-preserving systems
This page was last edited on 2022-08-25.
This page was last edited on 2022-08-25.
